None of us can sit totally on our laurels and think we’re safe from any hack on any website.
The hackers don’t care if we’re large or small, they just want to use our webspace. There’s been a lot of talk about what to do to protect ourselves from Brute Force attacks, and while we can do as much as we can, I don’t think it’s possible to protect ourselves from everything.
If we’re attacked by a botnet of about 90,000 addresses to choose from, we do need to try and do something to mitigate the risk to our blogs.
WordPress itself has done a lot of work to help us with this, and Matt Mullenweg who is the creator of WordPress has released a statement that outlines a fix we can all use to help ourselves.
What he said is more of less that WordPress 3 allows us to use custom names when we install our blogs and that we should be changing the default “Admin” username.
He said:
“Almost 3 years ago we released a version of WordPress (3.0) that allowed you to pick a custom username on installation, which largely ended people using “admin” as their default username. Right now there’s a botnet going around all of the WordPresses it can find trying to login with the “admin” username and a bunch of common passwords, and it has turned into a news story (especially from companies that sell “solutions” to the problem).
Here’s what I would recommend: If you still use “admin” as a username on your blog, change it, use a strong password, if you’re on WP.com turn on two-factor authentication, and of course make sure you’re up-to-date on the latest version of WordPress. Do this and you’ll be ahead of 99% of sites out there and probably never have a problem. Most other advice isn’t great — supposedly this botnet has over 90,000 IP addresses, so an IP limiting or login throttling plugin isn’t going to be great (they could try from a different IP a second for 24 hours).”
Looking at his advice, he recommends changing any username from admin to something else and making our passwords stronger. If Admin is the weak link, then change it we must. The admin login is set when we set up our blogs, and changing it is actually really easy.
I do have a login limiting plugin with Wordfence which I like, but it clearly isn’t enough on its own.
To Change your Admin username, or make a new one, simply follow the instructions.
- Login as your Admin User Account.
- Make sure your WordPress version is up-to-date.
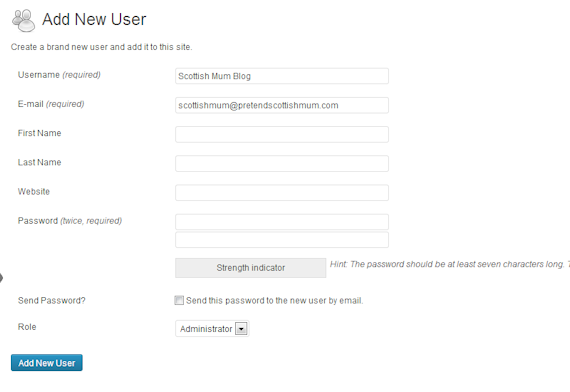
- Click Add New on the User tab in your dashboard.
- You will need a new e-mail address to set up a new user.
- Choose “Administrator” as the Role.
- Don’t choose a username that you are known by elsewhere. For me, choosing Lesley as a username would be weak as it’s my name and it’s on my blog for anyone to find.
- With your password, choose a difficult one with a mix of letters, numbers, symbols and both uppercase and lowercase letters.
- Don’t click to send the password by e-mail. The fewer places it goes online the better.
- Click “Add User”.
- Logout of your Admin Account and login as your new user.
- Go back to your User tab in your dashboard and click “All Users”
- Go to the Admin User and Hover above the name. You will see the option to edit or delete. Click to delete.
- It will give you the option to attribute all posts by the Admin User Account to another username. Choose your selection.
- Click “Confirm Deletion”.
That’s all you have to do to help keep your website a bit more safe from the Brute Force attack. If your logins are weak or easy to guess, go change them as fast as you can.

Definitely recommend removing the default Admin username. Limit Login Attempts and Login Lockdown are two additional plugins that can help improve the security of your blog.
Be sure to also keep your computer and browser up to date. WordPress has the browse happy project which has information on the latest web browsers.
Good info, it was!
I managed to figure this out a couple of weeks ago but it was not obvious, great post
Hopefully none of us get caught. I have been once and don’t look forward to it happening again anytime soon.
thanks! great post, just done mine.